Hackers have been exploiting two Windows vulnerabilities in the wild to escalate their privileges on compromised systems and gain access to sensitive data, bypass security measures, install backdoors, and even deploy ransomware.
The two zero-day flaws are tracked as CVE-2023-23397 and CVE-2023-24880, impacting Microsoft Outlook and the Windows SmartScreen security feature, respectively.
A zero-day vulnerability is a security flaw that is being actively exploited by hackers while the vendor of the impacted software doesn’t even know about its existence, let alone having written and released a fixing patch for it.
These vulnerabilities are called “zero-days” because this is exactly how long the software developers have to create and distribute a security update that addresses the problem.
In this case, Microsoft admitted yesterday that CVE-2023-23397 has been under active exploitation by a Russia-based threat actor, who used it in attacks against government, military, energy, and transportation organizations in Europe.
Information Microsoft shared privately with a limited set of customers indicates that the exploitation of this flaw has been underway since April 2022, reaching almost a full year.
The second flaw, CVE-2023-24880, was reported by Google as being actively exploited since at least January 2023, by the Magniber ransomware group.
Microsoft identified and addressed the two vulnerabilities on March 14, 2023, when the software giant released its monthly patch for supported Windows products.
Both are exploitable remotely and require no privileges, meaning that the attacker doesn’t have to compromise existing user accounts on the target system to leverage them.
Outlook easy to breach
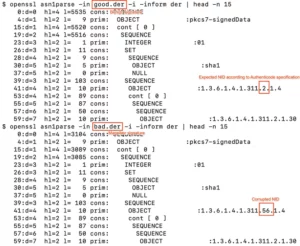
CVE-2023-23397 is a critical-severity vulnerability that allows threat actors to perform an NTLM relay attack, forcing a connection from the target device to an external UNC location. This results in stealing the victim’s hash, which the attackers use to authenticate as them.
By stealing email accounts, threat actors can access private information, perform internal phishing attacks on colleagues, and further their infiltration in corporate networks.
Unfortunately, CVE-2023-23297 is particularly easy to leverage, and a proof-of-concept (PoC) exploit was already released on the day of Microsoft’s disclosure by an independent security analyst, showcasing the flaw’s exploitation.
https://vimeo.com/808160973?embedded=true&source=vimeo_logo&owner=117332457
With the public release of this PoC, it is expected that adversaries will quickly incorporate it into their attack chains, targeting organizations that haven’t had the chance to apply the available security updates.
Zero-day ransomware attacks
The second zero-day flaw addressed this month is CVE-2023-24880, a security bypass flaw that allows attackers to create malicious MSI files that, when executed by the victim, won’t display the Windows Mark of the Web warning.
While this is a medium-severity flaw, Google’s Threat Analysis Group that discovered it, reported that it is being exploited by the Magniber ransomware gang, known for targeting the systems of large organizations or private individuals.
Google discovered the issue on February 15, 2023, when it reported it to Microsoft. However, it has indications that Magniber has been actively exploiting it since January 2023, counting over 100,000 downloads for the particular MSI files used in the attacks.
The fact that a medium-tier ransomware group was exploiting a zero-day vulnerability on Microsoft Windows is indicative of the ingenuity and determination of these financially motivated gangs.
MonsterCloud can offer professional ransomware removal and data recovery services for Magniber ransomware infections and all other malware strains currently in circulation, guaranteeing the seamless and quick restoration of mission-critical systems.
Additionally, MonsterCloud’s services include security advising and perimeter strengthening to prevent those catastrophic attacks from impacting your organization in the future.
Sources:
- https://msrc.microsoft.com/blog/2023/03/microsoft-mitigates-outlook-elevation-of-privilege-vulnerability/
- https://blog.google/threat-analysis-group/magniber-ransomware-actors-used-a-variant-of-microsoft-smartscreen-bypass/
- https://www.mdsec.co.uk/2023/03/exploiting-cve-2023-23397-microsoft-outlook-elevation-of-privilege-vulnerability/